KSL Investigates: How to prevent crooks from using your cell phone number to hack your identity
Apr 30, 2018, 10:15 PM | Updated: Feb 7, 2023, 11:20 am
SALT LAKE CITY, Utah – Cyber crooks have another way to steal your identity and money, take over your social media and get access to your personal information and financial records. It’s your cell phone number.
It even happened to the former Chief Technology Officer of the Federal Trade Commission.
In 2016, Lorrie Cranor told NBC News, “The idea that someone could steal my identity this way and that the phone company really didn’t do much to prevent it was something that was quite unsettling.”
Now it’s happening to a growing number of Utahns.
 Christina of American Fork told KSL in February that whoever had hijacked her cell phone account, got access to her text messages and had their eye on her bank account.
Christina of American Fork told KSL in February that whoever had hijacked her cell phone account, got access to her text messages and had their eye on her bank account.
“They were able to get online, on my accounts, and say ‘I had forgotten my username and passwords,’ and got a code sent to my cell phone,” Christina explained.
Many of us don’t think twice about typing our cell phone number into online forms, or giving it out to someone we hardly know. We link it to social media, bank accounts – even to our supermarket rewards cards. It may be time to rethink all that.
“They can do a lot more damage than they could in the old landline days,” says Robert Jorgensen, the director for Utah Valley University’s cybersecurity program. “They can use your phone number to fake text messages to people you know, maybe access your accounts.”
Jorgensen says criminals can easily find cell phone numbers by combing the web.
“A lot of them are buying a list phone numbers from some place that you’ve used it,” he explained.
Once they have a number, they’ll find out who it belongs to.
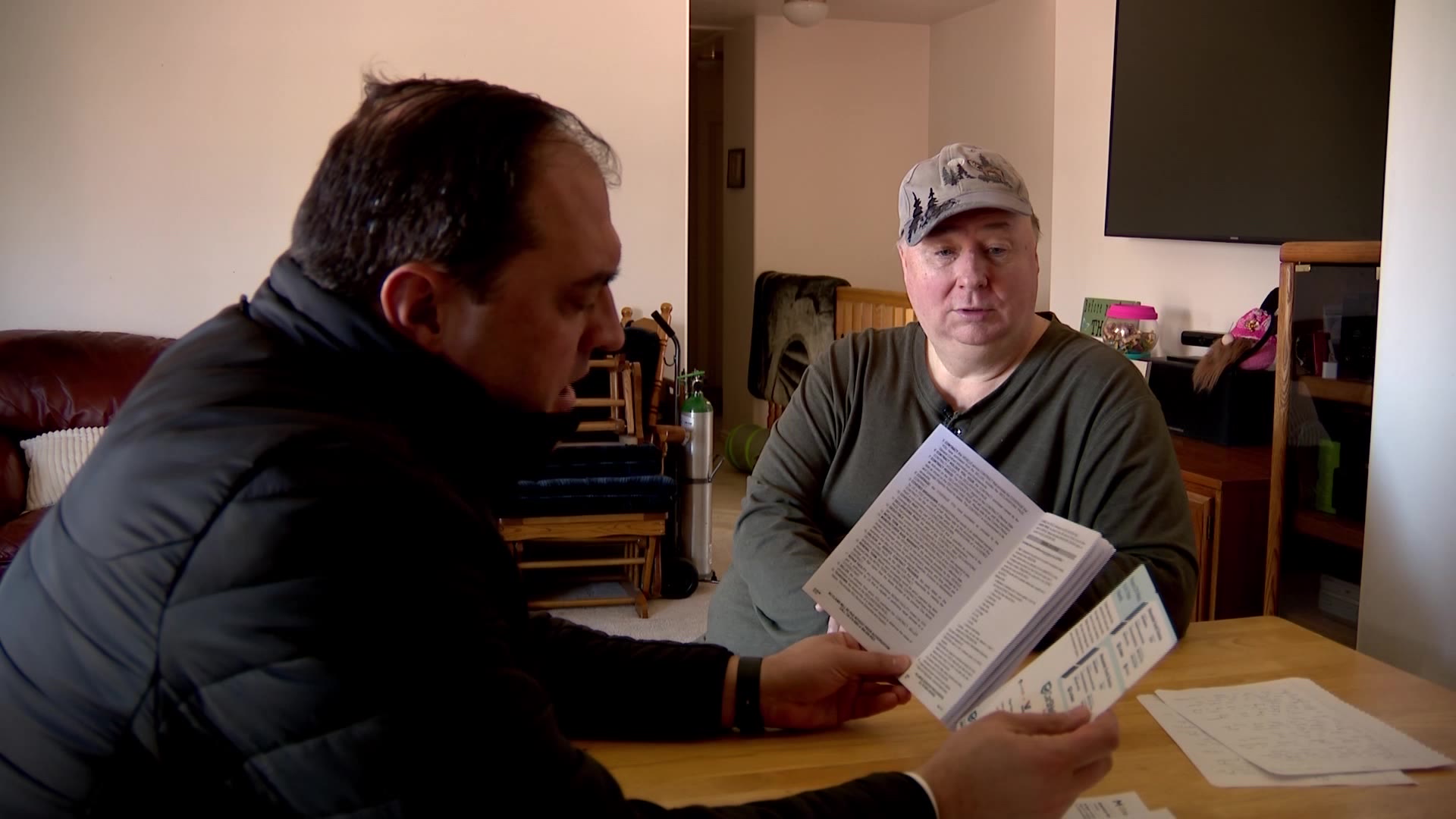
Rod Buhler of Salt Lake Community College’s cybersecurity program says a people search or reverse lookup site can spit out enough info to steal identities.
“Your name, obviously,” listed Buhler, “address, phone number, previous addresses, previous phone numbers, salary, who you work for.”
Buhler says with that info, a thief can call your carrier and pretend to be you to possibly get your service transferred to their phone.
From there, they can reset your passwords and intercept security messages from your bank, credit card company and others because they’re now getting your texts.
“If someone takes control of your phone, now they have control of that extra security level. So they can act like you and say, ‘Hey, send me that little security code and I’ll enter it in and I’ll take over your bank account and I’ll steal your money,’” Buhler explained.
How do you know if your number’s been hijacked? One giveaway is your phone stops working. It’ll say “No Service” or “Emergency Calls Only,” no matter how many times you restart it.
“If your phone stops working,” said Buhler, “call the phone company right away.”
To prevent your phone number from even being hacked, Jorgensen says you have to be careful where you put your phone number.
“Don’t put your phone number in places where it’s publicly accessible, and be careful who you give it out to.”
Both Jorgensen and Buhler recommend services like Google Voice, which offer a virtual phone number you can give out instead. Your phone still gets texts and calls, but your real number stays hidden.
Also, request a PIN or password from your mobile carrier account. It makes your phone account tougher to hack.
Fortunately for Christina, she found out her mobile account had been hijacked before the bad guys drained her bank account. Now, her mobile account is secured with a PIN.
“I think it’s scary because all of our accounts are tied to our cell phone numbers.”
SECURING YOUR ACCOUNT
The four major wireless carriers offer PINs or passwords for your mobile account, but you have to ask for it.
The exception is Sprint, it requires all customers to add a PIN and security questions when they open their account.
T-Mobile users can dial 611 on their phone, or call 1-800-937-8997.
AT&T users will need to add extra security through your account’s profile tab. Click Sign-in info, select your wireless account from the drop-down menu and then select Manage extra security in the Wireless passcode section. Check Extra security.
Verizon users can go vzw.com/PIN, call 1-800-922-0204 or bring your ID with you to a Verizon store.
BBB WARNING
The Better Business Bureau warned about the cell phone porting scam earlier this year. They provide additional advice for preventing identity fraud on their website.